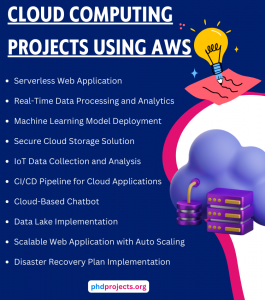
CLOUD COMPUTING PROJECTS USING AWS


CLOUD COMPUTING PROJECTS USING AWS
In the field of cloud computing, project topics and ideas are continuously evolving based on several important requirements. By carrying out in-depth exploration in cloud computing, we suggest numerous project plans, along with major AWS services and concise explanation that assist you to execute these plans in an efficient way:
- Serverless Web Application
- Explanation: With the aid of AWS services, a completely serverless web application has to be created. This web application could be relevant to a highly complicated task management system or a basic blog.
- Major AWS Services:
- In order to execute backend code excluding server allocation, use AWS Lambda.
- Develop, publish, and protect APIs with Amazon API Gateway.
- Accomplish a scalable NoSQL database using Amazon DynamoDB.
- For the combination of back-end and front-end, employ AWS Amplify.
- Specifically for static file storage, utilize Amazon S3.
- Result: Including a pay-per-use billing system, it offers cost-efficient, scalable web application.
- Real-Time Data Processing and Analytics
- Explanation: For various processes like ingestion, processing, and examining actual-time data streams, create an efficient pipeline. Processing clickstream data from a website could be the sample instance.
- Major AWS Services:
- Data ingestion in actual-time using Amazon Kinesis.
- Processing data streams with AWS Lambda.
- Storing processed data by employing Amazon S3 or Amazon Redshift.
- For data analytics and visualization, utilize Amazon QuickSight.
- Result: For data processing and analytics in actual-time, it provides an effective system. Based on live data streams, it also offers interpretations.
- Machine Learning Model Deployment
- Explanation: Using AWS for training and implementation of a machine learning framework. Categorization tasks could be included in this project, like customer churn forecasting.
- Major AWS Services:
- Create, train, and implement machine learning frameworks through the use of Amazon SageMaker.
- Storing datasets with Amazon S3.
- To execute inference in a serverless platform, utilize AWS Lambda.
- In order to reveal the framework as an API, employ Amazon API Gateway.
- Result: This project presents an implemented machine learning framework. For forecastings, this framework can be accessed through an API.
- Secure Cloud Storage Solution
- Explanation: By including different characteristics like access control, encryption, and frequent backups, a secure cloud storage solution must be deployed in terms of AWS.
- Major AWS Services:
- Attain scalable object storage with Amazon S3.
- Encryption key handling using AWS Key Management Service (KMS).
- For access control, employ AWS Identity and Access Management (IAM).
- Facilitating automatic backups through AWS Backup.
- Result: It provides a cloud storage solution in a manageable, credible, and secure manner.
- IoT Data Collection and Analysis
- Explanation: Plan to create a system, which employs AWS IoT services for gathering, processing, and examining data from IoT devices.
- Major AWS Services:
- Linking IoT devices with AWS IoT Core.
- Processing IoT data by utilizing AWS Lambda.
- To store IoT data, use Amazon DynamoDB.
- Employ Amazon QuickSight for data visualization.
- Result: To handle and examine IoT data, this project offers a scalable system.
- CI/CD Pipeline for Cloud Applications
- Explanation: For a cloud-related application, a Continuous Integration and Continuous Deployment (CI/CD) pipeline has to be developed.
- Major AWS Services:
- Automate the release process using AWS CodePipeline.
- Create and test code by employing AWS CodeBuild.
- To automate the application placements, utilize AWS CodeDeploy.
- Host the application with AWS Lambda or Amazon EC2.
- Result: It minimizes deployment faults and enhances creation effectiveness through an automated CI/CD pipeline.
- Cloud-Based Chatbot
- Explanation: Aim to develop an efficient chatbot, which is capable of offering services or details by communicating with users, like solving FAQs or reserving tickets.
- Major AWS Services:
- Create communicative interfaces with Amazon Lex.
- To manage the backend logic, use AWS Lambda.
- Recording session data by utilizing Amazon DynamoDB.
- Store static information using Amazon S3.
- Result: This project proposes a smart chatbot, which can be effectively combined with messaging environments or websites.
- Data Lake Implementation
- Explanation: As a means to store and examine a wide range of unstructured and structured data, build a data lake.
- Major AWS Services:
- Particularly for scalable data storage, employ Amazon S3.
- Consider data recording and ETL procedures (such as Extraction, Transformation, and Loading) with AWS Glue.
- For querying data that is recorded in S3 with SQL, use Amazon Athena.
- Handle complicated queries and data warehousing by utilizing Amazon Redshift.
- Result: Offers a data lake, which deals with extensive datasets and facilitates storage, querying, and analysis in an effective way.
- Scalable Web Application with Auto Scaling
- Explanation: Intend to create an efficient web application. In terms of requirements, this application must have the ability to scale automatically.
- Major AWS Services:
- For virtual server cases, use Amazon EC2.
- Specifically for handled relational databases, employ Amazon RDS.
- Adapt capability in an automatic manner with AWS Auto Scaling.
- To carry out tracking and recording processes, utilize Amazon CloudWatch.
- Result: To adapt resources on the basis of traffic, it suggests a more scalable and accessible web application.
- Disaster Recovery Plan Implementation
- Explanation: To assure business consistency in cloud-related applications, a disaster recovery strategy must be developed and applied.
- Major AWS Services:
- Automatic backup management with AWS Backup.
- For database backup and recovery, use Amazon RDS.
- In order to facilitate permanent storage of backup data, employ Amazon S3.
- To rapidly renovate platforms for infrastructure as code, utilize AWS CloudFormation.
- Result: For reducing data loss and break, this project provides an efficient disaster recovery policy.
Procedures to Execute Your Project:
- Define Goals: The major focus and purposes of your project have to be summarized in an explicit manner.
- Select AWS Services: On the basis of your project necessities, choose the suitable AWS services.
- Design Framework: Encompass in what way various services will communicate and design the framework of your project solution.
- Build AWS Environment: It is important to arrange your AWS platform. Then, the major services must be built appropriately.
- Create and Deploy: After that, you need to draft a code and set up significant services. Your project application has to be implemented.
- Testing and Validation: In order to assure that the project solution functions based on anticipations and aligns with the goals, you should assess the solution.
- Tracking and Optimization: To monitor performance and carry out major enhancements, employ AWS monitoring tools.
- Documentation and Depiction: By including processes, discoveries, and outcomes, create a report. Finally, plan for the project depiction.
What are some ideas for a final project in cloud security?
Cloud security is an effective approach that includes various techniques and measures for securing cloud-related data, application, and framework against different assaults. We recommend a few interesting project plans, which address different factors of cloud security and appropriate for final projects:
- Zero Trust Security Model for Cloud Environments
- Overview: To validate and authenticate each access request consistently in a cloud platform, apply a Zero Trust framework.
- Significant Aspects:
- Employ Google Cloud IAM, Azure Active Directory, or AWS IAM for Identity and Access Management (IAM).
- Incorporation of Multi-Factor Authentication (MFA).
- Utilize Azure Virtual Network, AWS VPC, or Google Cloud VPC for microsegmentation.
- With the aid of Azure Monitor, AWS CloudTrail, or Google Cloud Logging, carry out consistent tracking and logging.
- Result: In cloud platforms, it reduces the possibility of illicit access and lateral motion by creating an efficient security framework.
- Automated Cloud Security Compliance Auditing
- Overview: For cloud platforms, automate the compliance analysis with industry regulations (such as PCI-DSS, HIPAA, or GDPR) by creating a robust tool.
- Significant Aspects:
- Compliance strategies and architectures.
- Utilize Google Cloud Security Command Center, Azure Policy, or AWS Config for automated analysis scripts.
- Techniques for reporting and warning.
- Result: This project suggests a system, which minimizes the possibility of non-compliance issues by assuring consistent adherence to regulatory principles.
- Intrusion Detection and Prevention System (IDPS) for Cloud Infrastructure
- Overview: Across a cloud platform, track and identify illicit actions through the creation of an IDPS.
- Significant Aspects:
- Carry out analysis of network traffic by employing Google Cloud Packet Mirroring, Azure Network Watcher, or AWS VPC Traffic Mirroring.
- Machine learning for anomaly identification methods.
- Utilize Google Cloud Functions, Azure Logic Apps, or AWS Lambda for automated response techniques.
- Result: In the form of actual-time identification and response to possible hazards, it offers improved safety.
- Encryption and Key Management System
- Overview: In transition, working, and inactive states, an extensive encryption policy has to be applied for data, including efficient key management.
- Significant Aspects:
- Use Google Cloud KMS, Azure Key Vault, or AWS KMS for data encryption.
- For data transmission, implement end-to-end encryption.
- Strategies for creating, storing, and altering keys in a secure way.
- Result: Among the cloud platforms, it provides enhanced data morality and safety.
- Cloud-Based Honeypot for Threat Intelligence
- Overview: With the aims of identifying and examining malicious actions and collecting threat information in a cloud platform, build a honeypot.
- Significant Aspects:
- Utilize openly available tools such as Cowrie or Honeyd for Honeypot implementation.
- For tracking and logging, use Google Cloud Logging, Azure Monitor, or AWS CloudWatch.
- Investigation of data and threat intelligence alerts.
- Result: Offers enhanced security policies by providing interpretations on assault vectors and approaches.
- Secure Multi-Tenant Cloud Environment
- Overview: In a multi-tenant cloud platform, assure safety and isolation by creating an effective architecture.
- Significant Aspects:
- Employ containerization and virtualization mechanisms for tenant isolation.
- Implements Role-Based Access Control (RBAC) and access control strategies.
- For tenant-based actions, it enables tracking and logging.
- Result: To obstruct cross-tenant illicit access and data leakages, this project proposes an isolated and safer multi-tenant platform.
- Blockchain-Based Data Integrity in Cloud Storage
- Overview: As a means to assure data reliability and morality in cloud storage, implement blockchain mechanisms.
- Significant Aspects:
- Employ AWS Blockchain, Hyperledger Fabric, or Ethereum for blockchain ledger deployment.
- Facilitates incorporation into efficient cloud storage services such as Google Cloud Storage, Azure Blob Storage, or AWS S3.
- For automatic validation of data and morality analysis, use smart contracts.
- Result: By means of automatic validation and unchangeable logs, it suggests improved data reliability and morality.
- Cloud Security Information and Event Management (SIEM) System
- Overview: Specifically in a cloud platform, collect, examine, and react to security phenomenon through the creation of a SIEM system.
- Significant Aspects:
- Utilize AWS CloudWatch, ELK Stack (Elasticsearch, Logstash, Kibana), or Splunk for log gathering and aggregation.
- Interrelation and investigation of events.
- Techniques for incident response and warning.
- Result: This research facilitates incident response and enhances insight into security phenomena.
- Secure CI/CD Pipeline for Cloud Applications
- Overview: To guarantee code standard and security, a safer CI/CD pipeline has to be applied, including combined security analysis.
- Significant Aspects:
- Implements various CI/CD tools such as AWS CodePipeline, GitLab CI/CD, or Jenkins.
- Tools like Dynamic Application Security Testing (DAST) and Static Application Security Testing (SAST).
- Along with security verifications, it enables automatic deployment.
- Result: It specifically proposes a CI/CD pipeline, which minimizes risks in deployed applications and implements security-efficient approaches.
- Privacy-Preserving Data Processing Framework
- Overview: In order to process confidential data in the cloud platform without compromising confidentiality, create a robust architecture.
- Significant Aspects:
- Approaches for data anonymization and pseudonymization.
- Implementing differential privacy techniques.
- For safer data processing, use homomorphic encryption.
- Result: Suggests efficient system, which preserves confidentiality of data and compliance with rules in addition to supporting safer data processing.
Cloud Computing Thesis Using AWS
Doing research on Cloud Computing Thesis using AWS can be quite challenging for scholars. However, phdprojects.org offers a solution to this problem. Our team of highly skilled technical experts can assist you in completing your thesis efficiently and at an affordable cost. Simply provide us with your requirements and let us take care of the rest.
- Scheduling tasks based on branch and bound algorithm in cloud computing environment
- Optimization of Task Migration Cost in Infrastructure Cloud Computing using IMDLB Algorithm
- Task Scheduling Algorithm in Cloud Computing Environment Based on Cloud Pricing Models
- A graph and connected dominating set-based mathematical model for task mapping in cloud computing
- Trust Computation Framework based on User Behavior and Recommendation in Cloud Computing
- Diagnostic Lab Locator and Health Care System using Cloud Computing and Machine Learning
- An integrated framework for managing massive and heterogeneous sensor data using cloud computing
- A Hybrid Edge-Cloud Computing Method for Short-Term Electric Load Forecasting Based on Smart Metering Terminal
- Network Management in Cloud Computing for Public Administration: A Practical Use Case
- Discussion on Network Information Security Based on Cloud Computing Environment
- Formal Discussion on Relationship between Virtualization and Cloud Computing
- The framework for efficient passphrase-based multifactor authentication in cloud computing
- Task Migrations in a Cloud Computing Virtual Machine Using Cauchy Swarm Optimization Techniques
- Panel Data Fusion of Distributed Multi-Dimensional Data Index Strategy in Cloud Computing Environment
- Computation offloading frameworks in mobile cloud computing : a survey
- Performance evaluation of a green scheduling algorithm for energy savings in cloud computing
- An in-depth analysis and study of Load balancing techniques in the cloud computing environment
- Modeling and simulation of scalable Cloud computing environments and the CloudSim toolkit: Challenges and opportunities
- Energy efficiency for cloud computing system based on predictive optimization
- A systematic survey on energy-efficient techniques in sustainable cloud computing
Explore Related Research Topics
Discover additional academic services, research guidance, and publication support topics.
