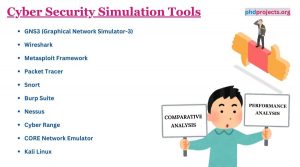
Cyber Security Simulation Tools


Cyber Security Simulation Tools
The following tools range from environments which simulate cyber threats in a controlled platform to network simulators for developing network activities on several criteria. Below, we provide an outline of a few main cybersecurity simulation tools with their utilizations:
- Wireshark
- Explanation: To catch and browse the traffic that is executing on a computer network communicatively, the users can make use of Wireshark which is a network protocol. It is vastly utilized for protection necessities like identifying malicious network behaviors and also for network troubleshooting, academics and observation.
- Metasploit Framework
- Explanation: For serving in penetration testing and IDS signature creation, and offering details about safety susceptibilities, a computer security project like the Metasploit project is beneficial. To enhance attention on protection, process remote threats and validate system sensitivities, it acts as an important tool for security experts.
- Packet Tracer
- Explanation: Packet Tracer is a network simulation and visualization tool which is constructed by Cisco Systems. To develop network topologies and replicate advanced computer networks, and for learning about network security solutions and protocols, this is more valuable to users.
- Snort
- Explanation: Snort has the ability of packet logging on IP networks and functioning practical traffic observation. It is considered as an open-source network intrusion detection system (NIDS). To identify different kinds of threats like stealth port scans, CGI threats and buffer overflows, this tool is utilized efficiently.
- Kali Linux
- Explanation: For penetration testing and digital forensics, Kali Linux is developed as Debian-oriented Linux dispersion. It consists of enormous tools especially for exploit creation, susceptibility scanning and network observation.
- Burp Suite
- Explanation: Burp Suite consists of different tools for functioning automatic scans and manual testing. To execute security testing of web applications, this tool can act as a combined environment. For revealing sensitivities in web application, creating it as an effective one.
- Nessus
- Explanation: Specifically for misconfigurations, approval with various safety regulations and sensitivities, Nessus is broadly employed as a susceptibility scanner which can scan different kinds of claims. It is important for generating documents on detected sensitivities and the process of reducing them, and also for evaluating susceptibilities.
- GNS3 (Graphical Network Simulator-3)
- Explanation: To simulate difficult networks by combining virtual and actual devices, GNS3 is an effective network software emulator which helps the users. Creating it perfect for safety protocols and network configurations before deploying them in a practical platform, it assists different network devices from sellers such as HP, Juniper and Cisco.
- Cyber Range
- Explanation: Particularly for cybersecurity training and software development, a Cyber Range is implemented as a virtual platform. To validate novel technologies against simulated cyber threats and get practical cyber skills, this offers a secure and authorized platform.
- CORE Network Emulator
- Explanation: Giving a practical setting for assessing network protocols and safety systems, designing network configurations, and validating situations by a tool called Common Open Research Emulator (CORE) which permits the development of virtual networks.
What is cyber security Research simulation?
Generally, the procedure of cybersecurity research simulation allows students, investigators and security experts to create ideas for defending, finding and reacting to cyber occurrence, validate novel protection techniques and get physical practice with cybersecurity theories in a clear way:
Objectives of Cybersecurity Research Simulation
- Threat Modeling and Analysis: To interpret the effect of cyber-attacks, activity and performance of protection ideas against them, simulate cyber risks effectively.
- Vulnerability Assessment: By simulating threats in a meticulous platform, detecting limitations in mechanisms, software and networks which can be misused by attackers.
- Security Training and Education: To build the cybersecurity knowledge like ethical hacking, forensics and incident response, offer a realistic learning practice for the experts and students.
- Testing and Assessing Security Solutions: In protecting against simulated threats, evaluating the performance of security configurations, protocols and instruments.
- Incident Response Planning: For rapid and efficient response to cyber events, designing and evaluating incident response strategies to confirm that the associations are ready.
Components of Cybersecurity Research Simulation
- Simulated Attack Environments: By enabling investigators to research threat methods and experiment protection systems, make use of tools such as Metasploit and Kali Linux to develop threat situations which imitate real-time cyber-attacks.
- Virtual Networks and Systems: Considering the effect of threats on network architecture and the research of network sensitivities, enable the development of digital networks which repeat difficult networking platforms using simulation software like Packet Tracer or GNS3.
- Cyber Ranges: For cybersecurity training and investigation, offer a communicative and practical platform through the generalized simulation environments. By providing an extensive platform for cyber experiments and rivalries, cyber ranges can simulate huge networks and IT mechanisms.
- Machine Learning and AI Models: To design adjustable safety machines, automate attack identification, and forecast attack activity, implementing AI and machine learning within simulations.
Applications of Cybersecurity Research Simulation
- Academic Research: In a secure and controlled platform, promoting the research of novel cybersecurity concepts, techniques and methods.
- Corporate Training: To experiment reacting to simulated cyber threats, improve the knowledge of cybersecurity groups in associations by enabling them.
- Policy and Strategy Development: By giving data on threat simulations, the efficiency of protection solutions and risk directions, help the creation of cybersecurity ideas and plans.
- Product Testing: On a range of simulated threat situations before market release, validate cybersecurity items severely with the assistance of vendors.
Cyber Security Simulation Tools Topics
phdprojects.org assist in more than 15+ Cyber Security Simulation Tools Topics contact us we will provide tailored assistance in any type of ideas you come up with. Comparative analysis, performance evaluation are done well by our developers, we share along with bench mark reference papers. Brief explanation will be shared until you are completely satisfied, we will provide you with guidance.
- Load-based dynamic flow scheduling in network security monitoring systems
- Network security management platform system design and implementation
- Security enhancement by detection and penalization of malicious nodes in wireless networks
- Analysis of Efficient Network Security using Machine Learning in Convolutional Neural Network Methods
- Research on Malicious URL Identification and Analysis for Network Security
- Apply Knowledge Map Technology to Improve the Security Level of Power Data and Network Information
- Construction of Network Active Security Threat Model Based on Offensive and Defensive Differential Game
- Improved priority queueing strategy in network security detection system
- Internet security games as a pedagogic tool for teaching network security
- Research on Computer Big Data Technology in Generative Countermeasures Network Security Protection
- Computer Network Information Security Threat Identification Technology Based on Big Data Clustering Algorithm
- The Design and Implementation of Software Defined Network Security Service Choreography System
- A Selection Strategy for Network Security Defense Based on a Time Game Model
- Status Quo Intelligent Evaluation of the Network Security Legal Awareness: Modelling and Simulations
- Managing Home Networks security challenges security issues and countermeasures
- Hierarchical and Complex Parallel Network Security Threat Situation Quantitative Assessment Method
- Development of penetration testing model for increasing network security
- Performance and manageability design in an enterprise network security system
- Design of Campus Network Security System Based on Network Information Security
- SDSEP: A Network Security Education Platform Based on Software-Defined Networking Technology
Explore Related Research Topics
Discover additional academic services, research guidance, and publication support topics.
