Master Thesis in Cyber Security


Master Thesis in Cyber Security
Cybersecurity plays a significant role in the digital era. phdprojects.org professionals assure you that our Cybersecurity thesis writing service will undoubtedly deliver a high-quality output. Rest assured, every aspect of your work will be thoroughly examined and refined to ensure that there is no trace of plagiarism. Together with possible topics according to current problems in the research domain, we suggest a summary about the formatted technique that assist in designing a master’s thesis in cybersecurity:
Structured Approach to Crafting a Master’s Thesis in Cybersecurity
- Topic Selection: It is approachable to select a topic that both fascinates you and also solves an important limitation or gap in the domain of cybersecurity. Typically, novel mechanisms, regulatory variations, evolving attacks, or certain divisions that are confronting specific cybersecurity limitations have to be determined.
- Literature Review: In order to comprehend the range of study on your selected topic, aim to carry out an extensive analysis of previous studies. It is significant to find gaps in expertise, debates, and the most current advancements.
- Research Question and Objectives: An explicit research query or theories that your thesis will solve should be designed. Certain goals have to be summarized in such a manner that directs your exploration and the range of your study.
- Methodology: It is appreciable to determine on the research methodology that better aligns with your chosen topic. Normally, this might be empirical setups, simulations, experimental study, or conceptual analysis. For replying to your research query, assure that your techniques are suitable.
- Data Collection and Analysis: Based on your selected methodology, gather and examine data. Qualitative data from case studies or interviews, quantitative data from experimentations, or incorporation of both might be encompassed.
- Findings and Discussion: The outcomes of your study have to be demonstrated and it is better to describe their significance. Investigate the relevance of your outcomes in the wider setting of cybersecurity, by contrasting your findings with previous studies.
- Conclusions and Recommendations: In this section, outline your major outcomes and their impacts. It is beneficial to provide suggestions for decision-makers, experts, or upcoming investigations according to your work.
- References: Following the suitable educational format, demonstrate an extensive list of every resource that you have mentioned in your thesis.
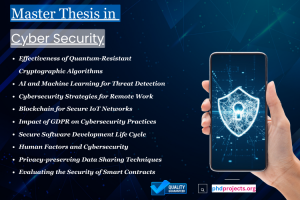
Potential Master’s Thesis Topics in Cybersecurity
- The Effectiveness of Quantum-Resistant Cryptographic Algorithms: Contrasted to cultural cryptographic algorithms, examine in what way quantum-resilient methods confront attacks of quantum computing.
- AI and Machine Learning for Threat Detection: Mainly, for identifying new cyber attacks such as complicated malware and zero-day exploits, aim to construct and assess machine learning frameworks.
- Cybersecurity Strategies for Remote Work: The cybersecurity limitations that are created by the raise in distant work should be examined. For protecting distant work platforms, concentrate on suggesting policies.
- Blockchain for Secure IoT Networks: In improving the confidentiality and safety of IoT networks and devices, investigate the purpose of blockchain mechanism.
- The Impact of GDPR on Cybersecurity Practices: Focus on evaluating in what way the cybersecurity policies and data security criterions in companies are impacted by General Data Protection Regulation (GDPR).
- Secure Software Development Life Cycle (SDLC): In order to avoid risks in software items, suggest a system for incorporating safety efficient ways during the SDLC.
- Human Factors and Cybersecurity: It is approachable to investigate in what way human aspects dedicate to cybersecurity violations. To improve user awareness and activities, aim to create valuable policies.
- Privacy-preserving Data Sharing Techniques: The approaches for sharing data among firms in a way that adheres to rules and conserves confidentiality should be researched.
- Evaluating the Security of Smart Contracts: On blockchain environment, explore risks in smart contracts and focus on suggesting algorithms for their safe implementation and advancement.
- Cybersecurity Policies for Emerging Technologies: For evolving mechanisms like 5G, augmented reality, or automated vehicles, construct extensive cybersecurity strategies, thereby solving certain safety limitations.
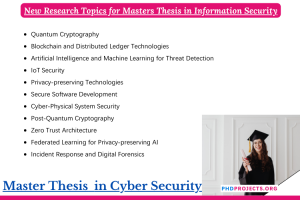
What are new research topics for a master’s thesis in information security?
There are several topics that are progressing in the domain of information security. Below are numerous ground-breaking topics in information security field that could be appropriate for a Master’s thesis:
- Quantum Cryptography: As quantum computing creates an important attack to recent cryptographic principles, research novel quantum-resilient methods and protocols.
- Blockchain and Distributed Ledger Technologies: The safety impacts of blockchain in different applications over cryptocurrencies, like supply chain management, identity authentication, and safer voting models should be investigated.
- Artificial Intelligence and Machine Learning for Threat Detection: To identify new malware, examine network congestion for abnormalities, and forecast possible violation of safety, concentrate on constructing AI and ML methods.
- IoT Security: Encompassing data confidentiality, device verification, and safe interaction protocols for IoT devices, solve the safety limitations in the Internet of Things (IoT) platform.
- Privacy-Preserving Technologies: In order to secure personal confidentiality in cloud computing and data analysis, study approaches like secure multi-party computation, differential privacy, and homomorphic encryption.
- Secure Software Development: For constructing software with in-build safety characteristics, it is better to examine algorithms and tools. To identify risks, encompass the purpose of proper algorithms, code analysis, and autonomous testing tools.
- Cyber-Physical System Security: The safety of the models that combine physical procedures with network computing, like smart grids, automated vehicles, and business control frameworks has to be concentrated.
- Post-Quantum Cryptography: Encompassing hash-related cryptography, multivariate polynomial cryptography, and lattice-related cryptography, focus on creating cryptographic frameworks that are safe in opposition to quantum computing assaults.
- Incident Response and Digital Forensics: Incorporating the usage of machine learning for anomaly identification, improve approaches for efficient incident response and forensic analysis in the outcome of safety violations.
- Federated Learning for Privacy-preserving AI: To instruct machine learning models on decentralized data, research the purpose of federated learning techniques, thereby conserving confidentiality when profiting from collaborative perception.
- Zero Trust Architecture: For applying zero trust safety infrastructures that consider no inherent trust outside or within network metrics, concentrate on constructing methodologies and systems.
- Advanced Persistent Threats (APTs) Detection and Mitigation: In order to identify, examine and protect against APTs, which are determined as complicated, extended assaults in opposition to certain goals, it is appreciable to investigate mechanisms and policies.
- Secure Identity and Access Management: To detect authentication, authorization, and verification in progressively complicated virtual platforms, aim to explore novel techniques.
- Ethical Hacking and Penetration Testing: Specifically, for ethical hacking, construct progressive approaches and tools to detect risks in networks and frameworks before they can be implemented by cyber attackers.
Master Thesis Topics in Cyber Security
In this article, you will find the most up-to-date Master Thesis Topics in Cybersecurity. Our team of experts conducts thorough research in various areas of Cybersecurity and effectively tackles the challenges associated with it. We adopt a strategic approach to overcome these challenges and provide valuable insights for your thesis. Just share with us all your ideas we will guide you with novel ideas and best thesis.
- Computer Network Information Security Analysis and Management Research Based on Neural Network
- Application research in computer network security evaluation based on genetic algorithm
- Improving Network Security and Performance by Multipath Routing in Ad Hoc Networks
- Technical Model of Computer Network Database Security Management Based on State Voting
- Research on the Application of Computer Artificial Intelligence Technology in the Field of Network Security
- Automatic Data Model Mapper for Security Policy Translation in Interface to Network Security Functions Framework
- The research on data flow technology in computer network security monitoring
- Analysis on solid protection system of industrial control network security in intelligent factory
- Research on Robustness of Network Security Vulnerability Detection Algorithm based on Recurrent Bayesian Networks
- Research on the network security of a web-based E-University system
- A Network Security Situation Element Extraction Method Based on Conditional Generative Adversarial Network and Transformer
- ACS: An efficient address based cryptography scheme for Mobile ad hoc networks security
- Novel method of assessing network security risks based on vulnerability correlation graph
- Design of network security early-warning system based on network defense in depth model
- Quantitative Analysis of Network Security Events Based Grey Relation
- Protection of Network Security Selector Secrecy in Outsourced Network Testing
- Systematic Deployment of Network Security Policy in Centralized and Distributed Firewalls
- A contemporary network security technique using smokescreen SSL in huddle network server
- Empowering Network Security With Programmable Switches: A Comprehensive Survey
- A LSTM-Based Method for Comprehension and Evaluation of Network Security Situation
Explore Related Research Topics
Discover additional academic services, research guidance, and publication support topics.
