Simulator Wireless Sensor Network


Simulator Wireless Sensor Network
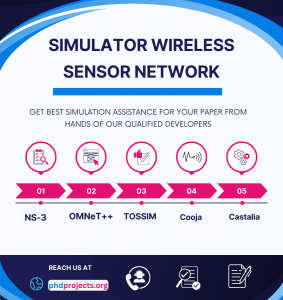
Several methods and simulators are useful for Wireless Sensor Networks (WSNs) projects. Appropriate for WSN-based projects, we list out a few prominent methods and simulators along with their major characteristics:
Simulators for Wireless Sensor Networks
- NS-3 (Network Simulator 3)
- NS-3 is generally a freely accessible network simulator.
- For WSN methods and protocols, it offers assistance.
- It is more adaptable and extensible.
- This simulator facilitates flexible and in-depth simulation contexts.
- OMNeT++
- OMNeT++ is referred to as a discrete event simulation platform.
- For developing conventional simulations, it acts as an extensible framework.
- Provides a wide range of assistance for network methods and protocols.
- Simulation of extensive WSN placements is supported by this tool.
- TOSSIM
- TOSSIM is particularly useful for TinyOS-related WSNs.
- It is highly scalable and effective.
- At the bit level, it supports the simulation of sensor network activity.
- Cooja
- Cooja facilitates the simulation of Contiki-related WSNs.
- It is specifically a phase of the Contiki OS platform.
- For assessing and debugging Contiki-based applications, it is very helpful.
- Castalia
- Castalia tool is relevant to OMNeT++.
- It enables the designing of wireless channel activity and actual physical operations.
- This tool is modeled, especially for body area networks and WSNs.
Methods for Wireless Sensor Networks
- Routing Algorithms
- LEACH (Low-Energy Adaptive Clustering Hierarchy):
- LEACH is a cluster-related protocol.
- To share energy utilization, it switches cluster heads.
- PEGASIS (Power-Efficient GAthering in Sensor Information Systems):
- PEGASIS is examined as a chain-related protocol.
- It minimizes the number of transmissions by transferring data from node to node.
- Directed Diffusion:
- It supports data-based routing.
- Through defining attributes, nodes require data.
- Localization Algorithms
- DV-Hop:
- For positioning, it utilizes the number of hop and average distance for each hop.
- RSSI (Received Signal Strength Indicator)-based Localization:
- On the basis of signal resilience, it evaluates distance.
- Range-free Algorithms:
- Generally, the accurate distance measurements are not considered by range-free methods.
- It utilizes hop-count and connectivity details.
- Data Aggregation Algorithms
- TAG (Tiny Aggregation):
- In TinyOS, it facilitates effective data aggregation.
- To minimize data transfer, it employs in-network processing.
- Synopsis Diffusion:
- It integrates data aggregation and multi-path routing.
- Useful for enhancing credibility and minimizing data redundancy.
- Energy-efficient Algorithms
- S-MAC (Sensor-Medium Access Control):
- Through periodic sleeping, it minimizes energy usage.
- B-MAC (Berkeley-Medium Access Control):
- Supports adaptive preamble sampling and low-power listening.
- TEEN (Threshold-sensitive Energy Efficient Network protocol):
- TEEN is examined as a hierarchical protocol with flexible thresholds.
- Security Algorithms
- SPINS (Security Protocols for Sensor Networks):
- It specifically offers novelty, data authentication, and privacy.
- TinySec:
- Useful for wireless sensor networks and is considered as a lightweight security framework.
- LEAP (Localized Encryption and Authentication Protocol):
- For various kinds of communication, it offers a diverse range of security.
Integrating Simulators with Algorithms
- NS-3 + LEACH/PEGASIS/Directed Diffusion:
- Supports the application and simulation of energy-effective routing protocols.
- Various performance metrics have to be examined, such as network durability, packet delivery ratio, and energy utilization.
- OMNeT++ + DV-Hop/RSSI-based Localization:
- It facilitates the simulation of localization methods.
- Consider the assessment of major metrics such as energy effectiveness, convergence time, and accuracy.
- Cooja + S-MAC/B-MAC:
- In this integration, we focus on evaluating medium access control protocols.
- Different significant parameters must be assessed, including throughput, latency, and duty cycle.
- Castalia + SPINS/TinySec:
- Our plan is to apply major safety protocols.
- On network performance and energy utilization, the implication has to be evaluated.
What are some hot topics in wireless network security one should do a thesis on?
Wireless network security is a major approach that focuses on securing computers and data by obstructing illicit access and data manipulation. Related to wireless network security, we suggest several topics which are latest as well as trending and also suitable for your thesis work:
- Security in 5G Networks
- Relevant to the 5G mechanism, we analyze the potential hazards and risks.
- To protect 5G interactions, create novel methods and protocols.
- In 5G networks, focus on data security and confidentiality issues.
- IoT Security
- Among IoT devices and the cloud platform, protect interaction.
- For resource-limited IoT devices, use lightweight cryptographic methods.
- IoT botnets and other malicious assaults have to be identified and reduced.
- Blockchain for Wireless Network Security
- To safeguard wireless network transactions, use blockchain mechanisms.
- Consider decentralized authentication techniques related to blockchain.
- For data morality and secure IoT interaction, utilize blockchain.
- Machine Learning for Intrusion Detection
- To identify intrusions and abnormalities in wireless networks, implement AI and machine learning.
- Create intrusion detection systems in a smart and flexible manner.
- Employ deep learning approaches for actual-time threat identification.
- Secure Communication in Ad Hoc and Mesh Networks
- For mesh and ad hoc networks, model safer routing protocols.
- Focus on applying trust handling architectures.
- In decentralized networks, assure data morality and privacy.
- Quantum Cryptography in Wireless Networks
- In wireless interactions, the use of quantum key distribution (QKD) has to be investigated.
- Consider the creation of quantum-resistant encryption methods.
- In combining quantum cryptography with previous wireless framework, we need to solve the potential issues.
- Privacy Preservation in Wireless Networks
- To protect user confidentiality in wireless interactions, explore methods.
- Focus on creating privacy-sensitive data aggregation techniques.
- In mobile networks, assure location secrecy and confidentiality.
- Security in Wireless Sensor Networks (WSNs)
- In WSNs, protect aggregation and sharing of data.
- For sensor nodes, explore energy-effective safety protocols.
- Various assaults like Sybil attacks and node capture have to be identified and obstructed.
- Security in Vehicular Ad Hoc Networks (VANETs)
- Among infrastructure and vehicles, assure safer interaction.
- Create vehicle authentication techniques in an effective and safer manner.
- In vehicular networks, solve issues relevant to confidentiality.
- Wi-Fi Security Enhancements
- For public Wi-Fi networks, enhance safety protocols.
- Wi-Fi-related assaults such as Man-in-the-Middle and Evil Twin must be identified and reduced.
- Our major concentration is to improve WPA3 safety protocols and characteristics.
- Edge and Fog Computing Security
- At the fog and edge layers, protect data storage and processing.
- For edge devices, we plan to create secure interaction protocols.
- In distributed computing platforms, assure data privacy and morality.
- Secure Network Function Virtualization (NFV)
- Against various cyber hazards, secure virtualized network functions.
- In NFC platforms, assure safer arrangement and handling.
- For harmed virtual networks, create isolation and containment approaches.
What are some thesis ideas about networking?
The networking thesis concepts deliberated among scholars are outlined below. Our expertise in thesis writing services surpasses mere assistance, extending to publication support. Benefit from editing and proofreading services provided by the team at phdprojects.org, ensuring a flawless final product. Share your ideas with us for expert guidance and support.
- Implementation of energy-efficent routing protocol within real time clustering wireless sensor networks
- Impacts Of Structural Factors On Energy Consumption In Cluster-Based Wireless Sensor Networks: A Comprehensive Analysis
- Performance Comparison And Analysis Of Proactive, Reactive And Hybrid Routing Protocols For Wireless Sensor Networks
- A Hierarchical Intrusion Detection Architecture For Wireless Sensor Networks
- Impacts of Structural Factors on Energy Consumption in Cluster-Based Wireless Sensor Networks : A Comprehensive Anal
- Automated Negotiation for Resource Assignment in Wireless Surveillance Sensor Networks
- An Energy-efficient Data Transmission Scheme in Underwater Wireless Sensor Networksysis
- On Synchronization of Wireless Acoustic Sensor Networks in the Presence of Time-varying Sampling Rate Offsets and Speaker Changes
- A Review on Secure Group Key Management Schemes for Data Gathering in Wireless Sensor Networks
- Intrusion prevention system using convolutional neural network for wireless sensor network
- Mobile agents assisted data collection in wireless sensor networks utilizing ZigBee technology
- Backscatter communications for wireless powered sensor networks with collision resolution
- Network Performance Enhancement with Optimization Sensor Placement in Wireless Sensor Network
- Application of Advanced Machine Learning and Artificial Neural Network Methods in Wireless Sensor Networks Based Applications
- Towards Clustering Technique for a Fault Tolerance Mobile Agent-Based System in Wireless Sensor Networks
- Network Performance Enhancement with Optimization Sensor Placement in Wireless Sensor Network
- An energy-efficient cluster head selection in wireless sensor network using grey wolf optimization algorithm
- Dynamic power allocation and scheduling for MIMO RF energy harvesting wireless sensor platforms
- Sensor Selection and Power Allocation Strategies for Energy Harvesting Wireless Sensor Networks
- Design of a Smart Custom Sensor Node Architecture for Wireless Sensor Network (WSN)
Explore Related Research Topics
Discover additional academic services, research guidance, and publication support topics.
